Wayne Sadin explores how public company and executive reports allow CIOs to delve into data lineage, opening the door for data modernization initiatives such as automation.
Search Results: cloud database (1163)
To build and maintain customer customer trust, businesses must understand how to identify and eliminate bias within their AI models.
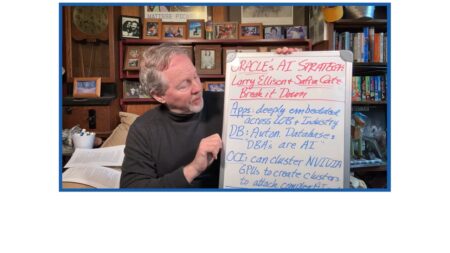
Oracle has laid out its new artificial intelligence (AI) strategy. Bob Evans shares details of this plan, including more intelligence and stronger business outcomes.
SAP’s new product, the SAP Datasphere, is a business data fabric architecture that provides data federation, data lakes, and data warehouses while preserving context.
CEO Safra Catz and CTO Larry Ellison have recently laid out a new strategy for Oracle that includes artificial intelligence and machine learning.
An in-depth look at automated vulnerability scanning within financial software, how it works, as well as top tools and best practices to get the job done.
Endor Labs released a report that identifies the top 10 open source software risks, including known vulnerabilities, compromised legitimate packages, untracked dependencies, and more. Chis Hughes explains.
Process mining offers great opportunity to fine-tune business processes but also introduces potential risks, which can be mitigated with strong governance measures.
Revolut tapped Couchbase software to help it fight evolving fraud attacks. The app it developed fought fraud and much more, netting millions in savings.
Bill Doerrfeld explains reveals why old-fashioned compliance practices can’t guarantee successful outcomes; real-time data and automation can help.
AI and automation can protect against financial and reputational losses from data theft and ransomware in financial software, writes Bill Doerrfeld.
Developers need guidance from CISOs to protect corporate data stores, ensure compliance, and spot disgruntled employees, and more, analysts Chris Hughes and Paul Swider explain.
A data governance framework is critical for an organization’s cybersecurity strategy. Frank Domizio explains why.
Data security strategy must go beyond securing a company’s data and employees to protect every data channel and counterparty. Wayne Sadin presents guidelines for managing third-party data risks.
Kieron Allen reviews a Databricks Lakehouse platform extension that lets developers build apps leveraging Databricks and Visual Studio functionality.
Knowing the types of data that cybercriminals target for identity theft, financial fraud, or other malicious activities helps security teams implement effective protection.
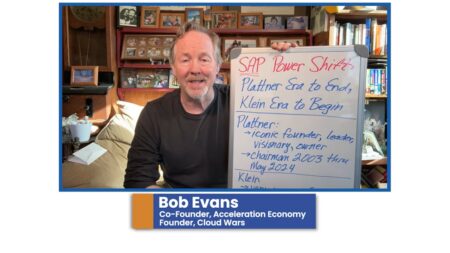
Bob Evans shares how SAP is taking on the ultimate transformation, after Hasso Plattner, Founder and Chairman, steps down from the company.
A power shift is taking place at SAP as founder and chairman Hasso Plattner steps down, allowing CEO Christian Klein to fully takeover as the single driving force behind SAP.
GitGuardian, a Cybersecurity Top 10 Shortlist company, offers a secrets detection platform that ensures source-code security for the DevSecOps era.
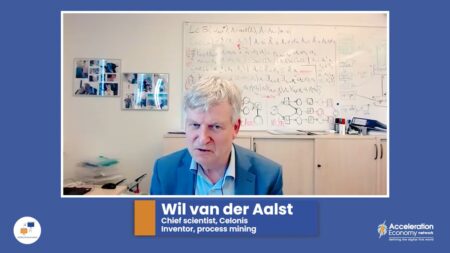
Prof. Wil van der Aalst explores current and potential use case for the latest form of the process mining technology he invented. He sees a bright future in supply chains and manufacturing.