After a breach, you’ll want to stop data loss as soon as possible, but it comes with risks and other drawbacks. Frank shares tips to arm you with the knowledge, options, and flexibility to advise your business on the right approach.
Search Results: data security (2134)
In this Data Modernization Battleground Moment, Okera CEO and CTO Nong Li highlights the challenges of data collection for organizations of various sizes.
In this Data Modernization Battleground moment, Chris says that cybersecurity professionals must understand data inventory, how businesses are using data, and who has access to data.
Acceleration Economy analyst and Paragon Films CIO Kenny Mullican shares data modernization tips from the tech executive’s perspective.
“Set it and forget it” assumptions can be dangerous when it comes to security. That’s why it’s important for users to understand everything their cloud tools can and cannot do.
Analyst Wayne Sadin offers ways for legacy organizations to update their data strategy so that they can keep up with cloud native organizations.
In Cybersecurity Minute, Ep. 29, Chris examines a recent data breach compromising the security software provider’s proprietary information.
The world is full of potential cyber threats. These best practices will help you be confident in your data privacy and security.
Cloud-based systems all have their own risks, which makes security particularly critical for SMBs in order to keep their data safe.
HYCU’s technology operates across enterprise and public clouds to give customers a flexible approach to data protection and backup.
In this Higher Education Battleground moment, Michelle Zeigmann identifies the benefits that California College of the Arts experienced with Workday.
Kylie Kiser discusses her upcoming sessions, sharing about how attendees can infuse AI as well as security in their Dataverse environment.
The company and ISV partners deliver agents that inject new functions into Copilot, Defender, and other Microsoft platforms, driving significant growth in the security ecosystem.
Microsoft data scientists share how AI is transforming cyber defense by enabling intelligent assistants that analyze attacks, suggest detection rules, and help organizations stay ahead of increasingly sophisticated AI-enabled attackers.
Mark Polino explains why businesses must rethink security roles, implement strict guardrails, and proactively design policies for an AI-driven environment.
As enterprises require AI models to deliver consistent, secure performances on a regular basis, organizations need an AI-ready security foundation that protects their data, meets regulatory demands, and brings order.
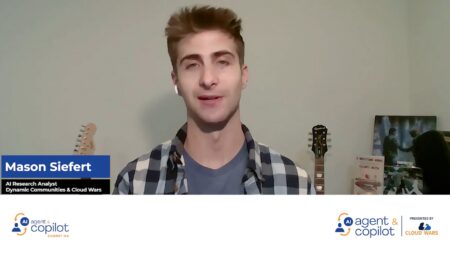
Mason Siefert explores how Microsoft is advancing enterprise security from traditional detection to AI-powered investigation and response.
Herain Oberoi highlighted two fundamental AI-Era cybersecurity questions: Can we trust the data, and is the AI system safe and secure? These concerns underpin Microsoft’s integrated governance and security strategy.
Security Dashboard for AI is built to rein in AI sprawl with Defender, Entra, and Purview integration as well as inventory functions that span Microsoft and widely used third-party AI software.
By combining AWS AI capabilities with NTT DATA’s delivery scale, the partnership accelerates legacy modernization and responsible AI adoption in highly regulated sectors worldwide.