For CISOs and security leaders, grappling with the global ramifications of the EU AI Act becomes paramount, necessitating a proactive stance.
Frank Domizio explores how IT leaders can ensure their organizations are protected from security threats in a way that also enables business growth.
A look at new guidelines for secure AI system development released by the Cybersecurity Infrastructure and Security Agency and the National Cybersecurity Center in the UK, emphasizing a holistic approach throughout the software development lifecycle.
Chris Hughes explains why sharing insights from threat intelligence with other senior execs can be a force multiplier in reducing organizational risk.
Wiz’s AI Security Posture Management (AI-SPM) addresses security and privacy concerns wrought by AI with comprehensive oversight, inventory management, and misconfiguration checks.
In this guidebook, practitioner analysts and CISOs define how to craft a secure foundation for businesses to thrive in today’s ever-changing digital economy.
Organizations must consider the security and privacy implications around using generative AI apps and large language models.
NetRise introduces Trace, an AI-powered feature revolutionizing software supply chain security, employing natural language processing to proactively identify and validate compromised assets and map relationships across the software supply chain.
Is AI genuinely a crucial component of a cybersecurity offering? CIO Kenny Mullican explores what existing practices look like with and without the technology.
NetRise’s AI-driven Trace feature transforms supply chain security, using semantic search and natural language processing to identify risks, offer context-rich insights, and create comprehensive asset graphs.
Establishing a strong working relationship between the CISO and the CIO is crucial for the overall success and security of a company, writes Kenny Mullican.
HYCU reaches SaaS data protection milestone with 50th integration, continues to ramp up protection for AWS environment.
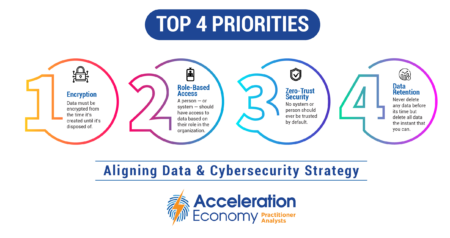
The chief data officer (CDO) and chief information security officer (CISO) should agree on encryption, role-based access, zero trust security, and data retention for effective business decisions and risk mitigation.
This guidebook offers insights into
the challenges of hybrid work in the cloud era, the strengths and weaknesses of traditional
cybersecurity mechanisms aimed at addressing those challenges, and why organizations need a CASB with DLP to control access and protect data at a granular level.
AI Index Report Ep 16: HeyGen uses AI and deep fakes for language translations; Wraithwatch gains funding for generative AI threat detection; and Microsoft launches its lightweight phi-1.5 model.
Managed services take center stage at the Cisco Partner Summit, capturing attention as a pervasive theme with over 80% of partners embracing the evolution.
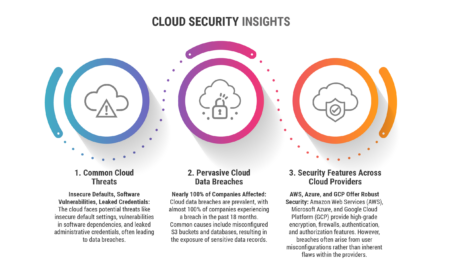
The big three cloud service providers AWS, Azure and Google Cloud share but also differ on features and vulnerabilities.
At first glance, cybersecurity models among cloud providers may seem like near carbon copies of each other, but a bit of digging can yield some real differences.
Learn the three main ideas behind zero trust packet routing, which involve bringing identity to the cloud, automating policy creation, and emphasizing ongoing policy adaptability.
Oracle EVP Mahesh Thiagarajan gives insight on the company’s goals with cloud network security and its zero-trust platform.