In this Back @ IT episode, Aaron hosts a conversation with Robert Wood to discuss how a cybersecurity framework can add value.
Cybersecurity
The backdrop of big data has changed the relationship between the IT department and Business Analysts across data, cloud, and cybersecurity.
As there is much excitement about the emerging virtual world, many still can’t help but question the level of security in the Metaverse.
Multi-cloud services are often associated with their own identities, permissions, authentication, and authorization activities.
In this Cybersecurity Minute, Chris discusses action being taken by the SEC to ensure cybersecurity expertise at the board level.
Data from Cloudflare exposes the top threats facing today’s web applications, including HTTP malformed requests, insecure API, & bots.
In this Cybersecurity Minute, Chris reports an advisory from federal agencies warning about nation-state hackers.
Security monitoring is one part of an overall effective security strategy. What tools will compliment your organizations strategy?
Identity has become the new perimeter in modern Zero Trust aligned environments. So, what are the fundamentals of digital identity security?
Organizations that invest in data privacy encounter a major opportunity to build trust with their customer bases and partners.
When looking at the Cybersecurity market, these top players stand out amongst competitors. What makes them unique in this industry?
The evolution of the Microsoft partner program brings the cloud and customers front and center, and unlocks new potential for CXOs
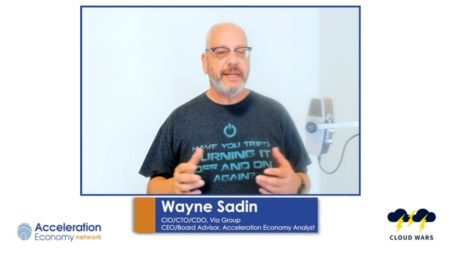
In this Future CXO Minute, Wayne explains how multi-factor authentication is a key security component and why CXOs should prioritize it.
What role should the CISO be reporting to? What key activities will they have oversight and provide expertise on?
2022 Top trends for ML: IoT, Cybersecurity, MLOps, GANs, Low-Code No-Code, smart RPA or Ethics in Artificial Intelligence.
In this Enterprise AI Minute, Aaron uses C3 AI as an example of how AI has moved to the frontlines of cybersecurity and what this means for your organization.
With the risk of Ransomware increasing, organizations need to apply this guidance to prepare and prevent attacks.
Cybersecurity must evolve to meet unknown threats. Here’s how artificial intelligence and machine learning will transform cybersecurity.
In this Cybersecurity Minute, Chris discusses the recent cyber attack on Samsung and the result of the source code being leaked.
In this Cybersecurity Minute, Chris Hughes highlights Google Cloud’s recent acquisition of Mandiant to provide greater cloud cybersecurity offerings.