Since the development of computers and phones, we began producing documents containing data, such as word documents, PDFs, spreadsheets, pictures, videos, and more. As we produce more digital assets, we feel the need to implement security, especially when the assets contain data.
In this case, the sense of security has always been connected to a sense of ownership or possession – because possession creates the feeling of control. That’s why we store all of those documents in our own local systems—laptops, hard drives, USB drives, external drives, cell phones, etc.
When we use the cloud, in its many versions and applications, and the feeling of control—hence security—gets tied up with a user and password.
However, we know that the cloud is something that we don’t possess. That creates a weak feeling of security towards cloud storage, as data and files are stored somewhere else where we can only access, but don’t own.
In addition, we have witnessed news about sensible data being leaked from many companies in recent decades. So, it is natural to question, “Is data that’s stored in the cloud secured?” and “Is my personal and company data secured in the cloud?”
Data in the Cloud vs. Local Systems
Information in the cloud is likely to be more secured—sometimes a lot more secure—than in your own local systems or devices. Cloud providers add more robust cybersecurity layers than regular users on local systems or devices.
Yes, it is true that a device or system can have great layers of security in place protecting data and files stored in it that can be as good as the cloud. It is also true that not all cloud services or providers are the same in terms of security.
However, if we add security measures systems and devices to protect locally stored data, it becomes a burden to the user to access that data. In contrast, by accepting any cloud default security measures, data is protected with a lot more than just ‘user and password’.
How Data Can Be Stolen
Now, let’s explore the other side: how cyber attackers can steal data. There are many ways to do it, but believe it or not. Still, the most common way to steal data or gain access to data is by social engineering. For instance, this can include phishing emails, fake impersonation, or malicious links and files with malware.
How Data is Secured in the Cloud
In any cloud nowadays, data centers—physical locations of cloud storage—are not accessible by cloud provider employees and workers. They are supervised by third parties. Also, all data is fully encrypted. Security applications and patching are constantly updated, even before these updates are released to the massive public.
Additionally, there are several firewalls. What’s more important: data and files are ‘ultra-backed-up’. Almost anybody can activate Two-Factor Authentication (2FA). When access to data has been made from a location or device, it can be expected to receive a notification from the app about it. As users, we can continue or shut down the suspicious access.
Final Thoughts
My personal laptop does not have all those security measures by default, not even my cell phone, where I take all my personal and professional calls, messages, pictures, and surf the web. Adding extra security to a personal device or local system is not that easy. It can often be costly. Not to mention the many actions needed to take every time it is necessary to access data and go through all the security.
If you are working with data in the cloud or planning to do it—and I advise you to do it—work with your provider or read the recommendations to be well informed about the security measures in place and how to improve security in the cloud service.
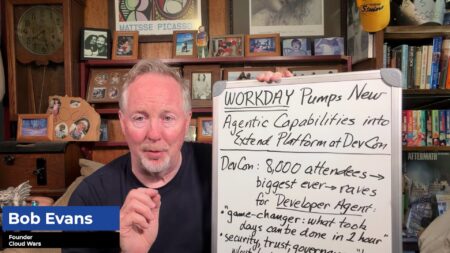
REGISTER TODAY TO EXPERIENCE HOW DATA FUELS THE ACCELERATION OF DECISION-MAKING AT CLOUD WARS EXPO