Wayne recaps Data Modernization Battleground sessions with Teradata and Okera, which discussed their data analytics for multi-cloud and data security solutions.
Cybersecurity
From hackathons and gamification to champion programs and callouts, there are many ways for security teams to build essential relationships with development teams.
Janet looks at this year’s Verizon Data Breach Investigations Report (DBIR) and singles out a few facts that can help organizations evaluate risk in partnership strategy.
Chris provides takeaways from the Cyber Safety Review Board’s recent Log4j incident report.
Bill Doerrfeld speaks with oak9 Co-founder Aakash Shah about ways to reduce known and unknown vulnerabilities brought on by open-source software.
As Bill explains, continuous delivery/deployment scenarios require special and specific security — especially in industries that handle sensitive personal and financial data.
Penetration testing is an inherently manual process and runs in contrast to the DevSecOps movement, so where does it fit in? Robert Wood delves into it.
It’s common for the C-suite to look at cybersecurity efforts with fear, uncertainty, and doubt (FUD). Here’s why that needs to stop, and how to do it.
Managing AI bias empowers organizations to unlock AI’s tremendous opportunity to drive positive outcomes, writes Robert Wood in this look at the new NIST AI playbook’s main takeaways on the topic.
In this CloudWorld News Desk interview, Oracle Senior VP of Cloud Infrastructure Mahesh Thiagarajan explains why some users are still reluctant to engage with multi-cloud platforms.
Quantifying cyber risk helps board members and other business leaders see the importance of cybersecurity investment. As Chris Hughes explains, the FAIR model offers a framework to do this.
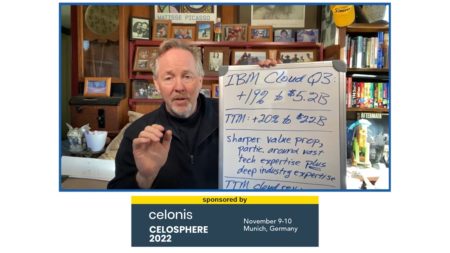
Bob Evans explains how CEO Arvind Krishna’s intense focus on the cloud and AI has transformed IBM into an innovative and disruptive contender.
In this episode, Bob Evans says that CEO Arvind Krishna deserves huge credit for the leadership and unification he has brought to the company, which has made it easier for customers to engage.
Doing things the way they’ve always been done is never a good strategy where technology is concerned, and security is no exception, writes Robert Wood.
What’s in a vulnerability score? Chris Hughes explains what these are, where they come from, and how cybersecurity professionals should approach them.
Robert Wood explores several areas of risk that can emerge with the adoption of low-code/no-code applications.
On location at Oracle CloudWorld, Bob Evans discusses Oracle’s impressive positioning, thanks to last quarter’s 45% cloud-revenue growth rate.
There’s a big push for SBOMs (software bills of material) as it’s becoming clear how crucial they are to cybersecurity. Read our guidebook to learn everything about SBOMs, including what they are and why they’re necessary, and how they work.
It’s often said that security must be baked in rather than bolted on, and this is especially true when it comes to CISO involvement in an organization’s data governance plans.
In episode 31, Chris Hughes explains the NSA’s recent release of software supply chain security guidance for developers.