By using proven practices, you can set the right foundation for a meaningful sustainable procurement program that helps your organization meet its goals in this area.
Search Results: data governance (723)
The big change of zero trust can be intimidating to some, but security leaders can tailor their communication to make the shift more palatable.
Small- and medium-sized businesses can stay current on the latest threats and detect and prevent attacks with tailored threat intelligence data by leveraging open-source platforms, tools, and communities.
Welcome to the first episode of “Generations,” in which practitioner-analysts from the Gen Z, Millennial, Gen X, and Baby Boomer generations discuss important tech topics.
Security teams can assist with financial automation projects that often require third-party tools. Rob Wood has some tips on how to select them.
Embracing digital transformation, cybersecurity, energy-efficent infrastructure, and relevant data and systems helps meet sustainability goals.
With its low-code platform, Appian empowers customers to build applications that automate key business functions. It’s prepared to guarantee their success.
The first day of the Digital CIO Summit was filled with first-person perspectives and practitioner-led sessions about the role of the CIO.
By using AI frameworks, companies can ensure transparency, compliance, and more, which will lead to building customer trust in AI systems.
Healthcare companies can benefit from platform engineering to build and ship applications faster while retaining governance guardrails around development.
Grip Security addresses the challenges of SaaS security by providing tailored insights and an agentless deployment mechanism among other advantages.
There are many benefits to using the zero trust maturity model as a framework for cybersecurity planning and implementation, say Rob Wood.
As sustainability becomes a key focus for businesses and critical infrastructure, organizations must also prioritize cybersecurity and secure data standards to safeguard emerging technologies like IoT and OT devices from evolving cyber threats.
Kenny Mullican escribe las múltiples ventajas y beneficios de una estrategia multi-nube sobre la operación de la cadena de suministro.
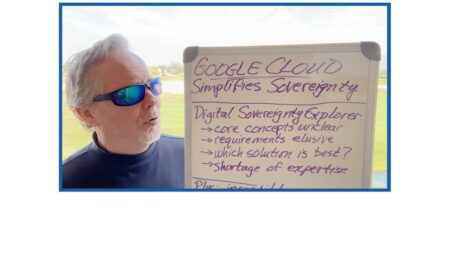
Google Cloud has introduced a simple, powerful online tool to help businesses optimize their data-sovereignty initiatives, namely titled Sovereignty Explorer.
How does Google Cloud plan to simplify data sovereignty? With its latest product, Digital Sovereignty Explorer, explains Bob Evans.
Though it makes for complex sourcing, healthcare cloud migration can be successfully approached with some classic procurement techniques, writes Joanna Martinez.
Maturity models serve as roadmaps to help organizations successfully navigate their zero-trust journey. Rob Wood breaks down the benefits of one model’s iterative approach.
Environmental, social, and governance frameworks are on the rise, and they must be crafted with enough security considerations to ward off increased cyber threats.
Multi-cloud computing allows organizations to tailor their cloud strategies, reduce costs, and avoid vendor lock-in, but it also brings unique cybersecurity challenges.
Our Securing Multi-Cloud Ecosystems guidebook is a comprehensive resource demonstrating the why & how of secure multi-cloud computing.