In this special interview, Aaron Back speaks with Kenny Mullican about the top trends and takeaways from last week’s IBM Think 2023 event in Orlando.
While generative AI is still a relative newcomer in the channel, it’s already starting to create an impact in several ways.
Leveraging threat intelligence for operational needs can make organizations more effective and adaptable in modern cybersecurity operations.
The new resource provides intelligence on malicious actors and attack vectors, especially those used in recent software supply chain attacks.
A communications point person is essential after a breach; they keep everyone in the loop, enabling cybersecurity folks to focus on cybersecurity.
Working with multiple partners delivers the best outcomes for enterprises looking to integrate critical elements of modern business infrastructure.
From watsonx and will.i.am to co-creation and creativity, the first-day news, topics, and presentations at IBM Think were timely and thought-provoking, says Kenny Mullican.
Organizations need to invest in the right people, processes, and technologies to protect themselves from online threats in particular.
Lookout Chief Strategy Officer Aaron Cockerill explains how DLP helps CEOs and CISOs optimize cybersecurity in SaaS environments.
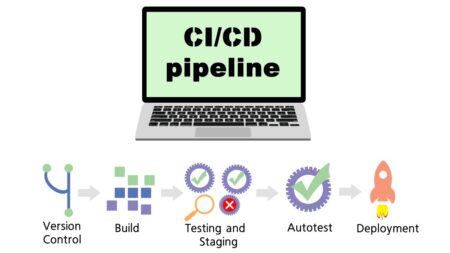
Bill Doerrfeld analyzes the state of modern CI/CD security, reviews the most common risks, and offers some safeguarding suggestions.
In this CIO Summit moment, Microsoft WW Sustainability Industry Advocate Matthew Sekol discusses the intersection of sustainability, risk, and ESG.
On location in Orlando at IBM’s annual conference, Kenny Mullican shares his short list of conference highlights this week in this preview.
A briefing featuring three CISO Practitioner Analysts discussing the state of the market, CISO priorities, Multi-Cloud Cybersecurity, SaaS Security, and the impact of Generative AI.
Contextualizing your organization’s key risks and general technology trends with peers is the best way to prepare against future security threats.
Networking opportunities and the need for integrated solutions were crucial takeaways of RSA 2023, along with the increasing complexity of the cybersecurity landscape.
Acceleration Economy along with Google and Microsoft introduce the Generative AI Digital Summit, featuring insights from industry leaders and practitioner analysts.
Excerpted from the session on “AI, Cybersecurity, and Innovation,” this CIO Digital Summit moment features a cautionary tale about what caused a security breach at the SBA.
Cybersecurity teams must work closely with finance teams to help them determine what kind of data is essential for automation to deliver more benefits than risk.
Cybersecurity vendor GitGuardian launches a new module aiming to draw software supply chain intruders in, then capture their information.
Fear, uncertainty, and doubt (FUD) surround AI in cybersecurity, and practitioners need to have proactive conversations to combat it.